Updated script available at https://www.rushworth.us/lisa/?p=6854
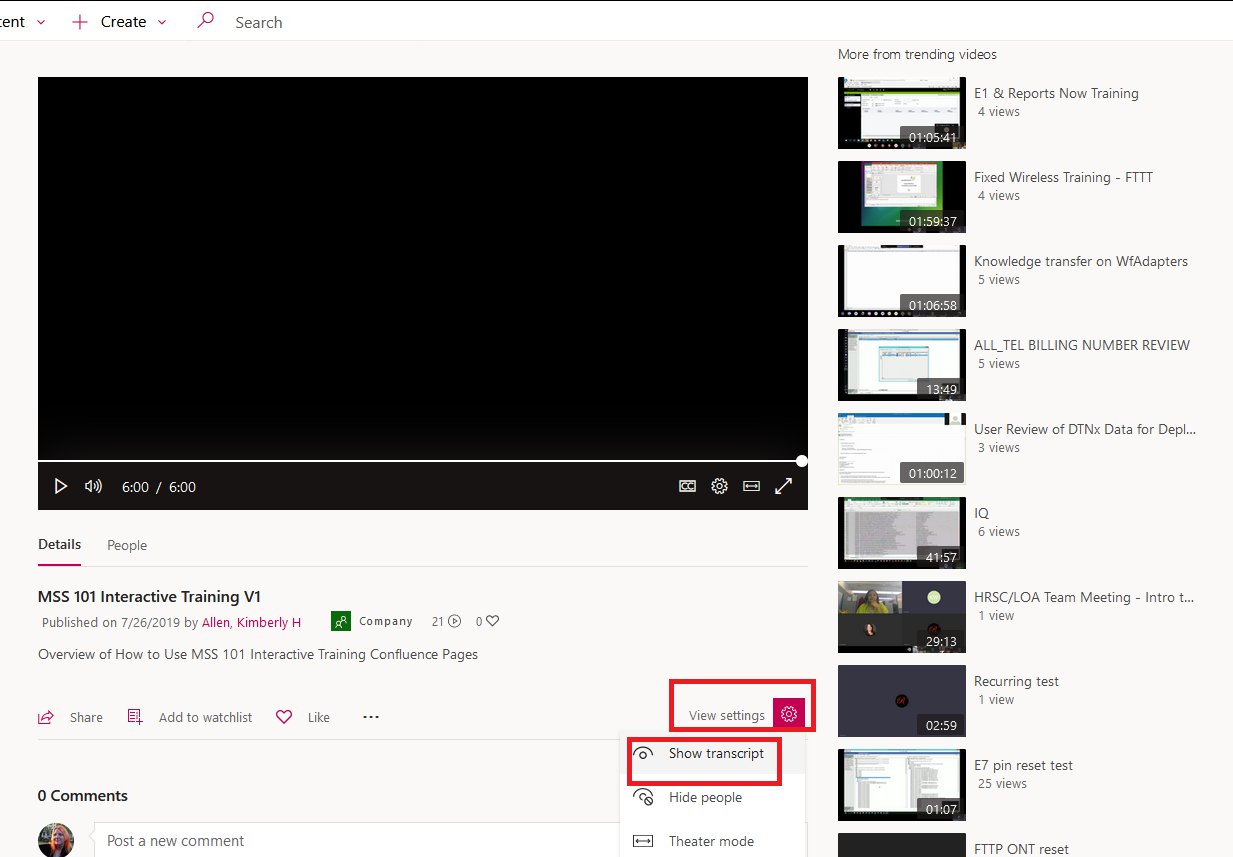
While Microsoft does not provide a way to export the transcript from Stream videos (thus recorded Teams meetings), it is possible to get something a nicer than the select/copy/paste from the transcript box. Click the video settings and select “Show transcript”
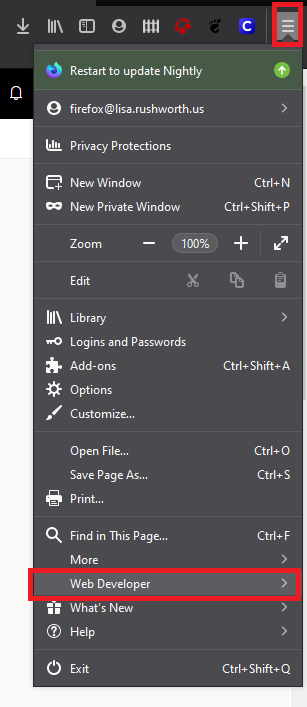
Display the browser developer tools – In Firefox, select the “Web Developer” sub-menu from the browser menu and select “Web Console”
This console is often used for displaying errors in a website, but it can also be used to send commands to the browser. There’s a “>>” prompt – click next to it and you’ll have a flashing cursor.
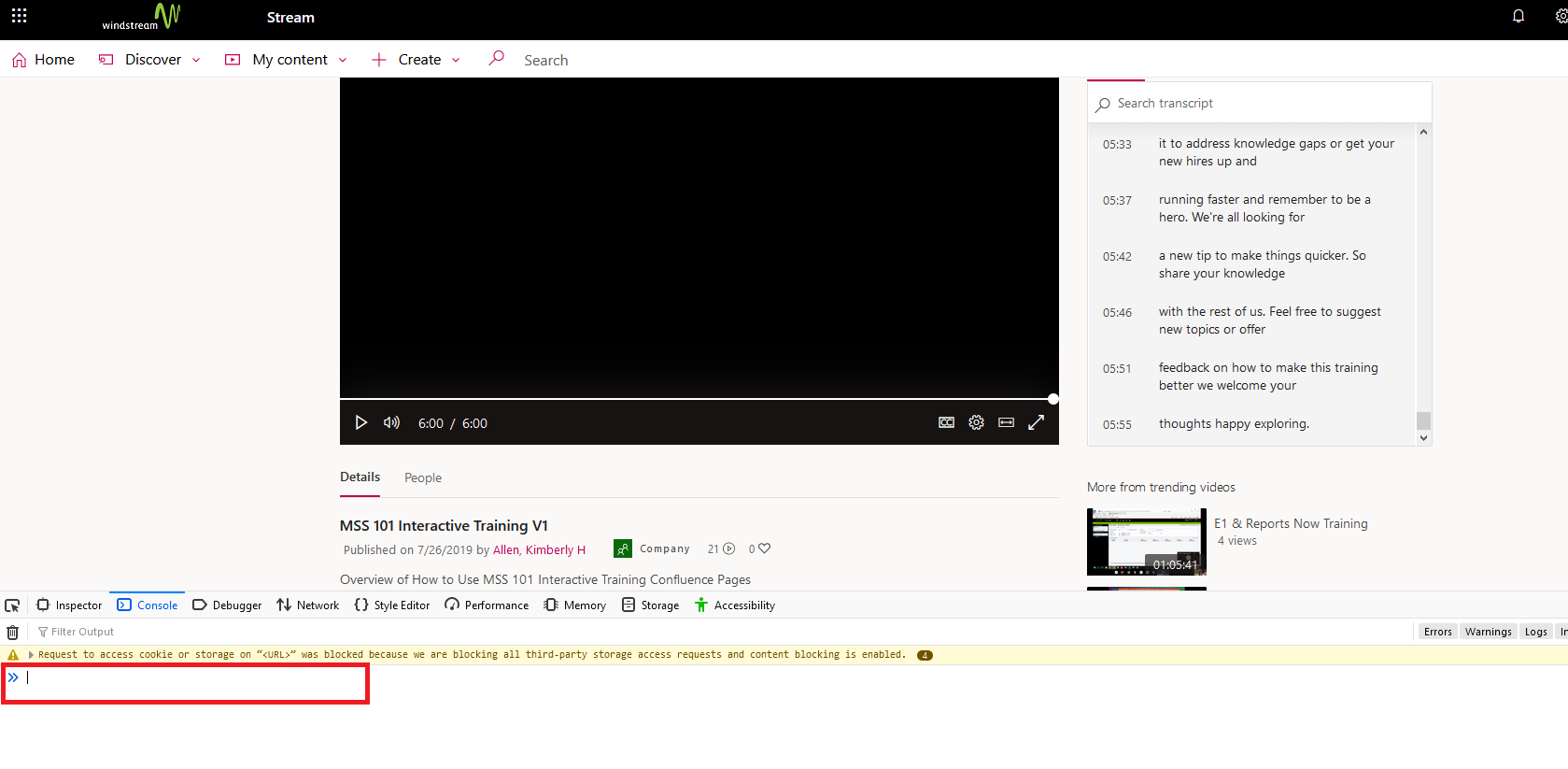
Paste this into the console:
window.angular.element(window.document.querySelectorAll('.transcript-list')).scope().$ctrl.transcriptLines.map((t) => { return t.eventData.text; })
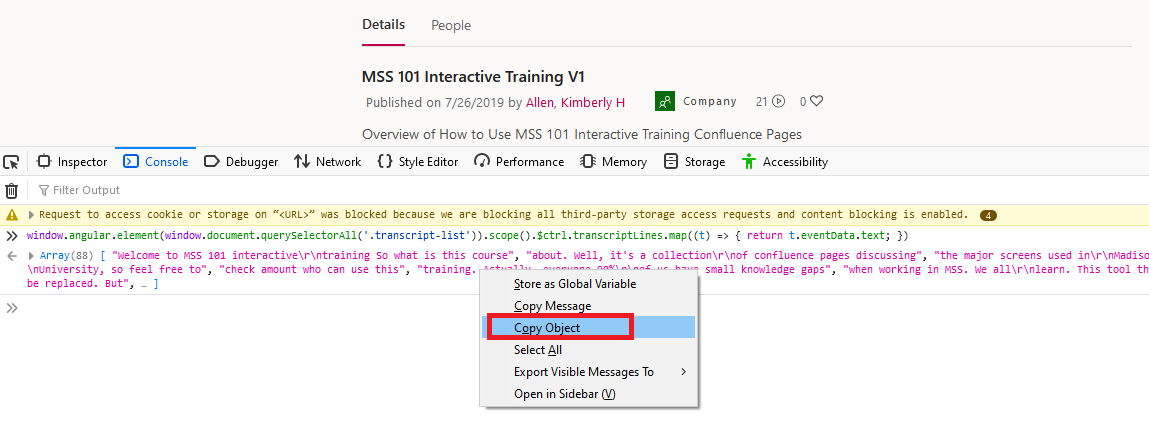
… and hit enter. Another line will appear below what you’ve entered. Right-click on that new entry and select “Copy Object”. Now paste into a text editor or Microsoft Word.
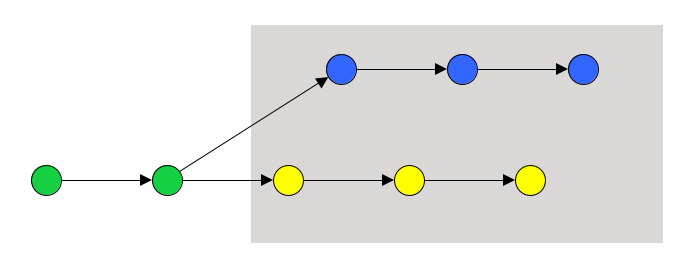
The output could use a little cleanup. You’ll see “\r\n” anywhere there’s a newline. This
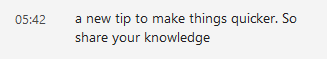
Becomes “a new tip to make things quicker. So\r\nshare your knowledge” … you could replace “\r\n” with a space (I find the newlines to be superfluous) or use a regex replacement to replace “\\r\\n” (literal string, the backslash escapes the backslash to retain it) with “\n” (an actual newline)
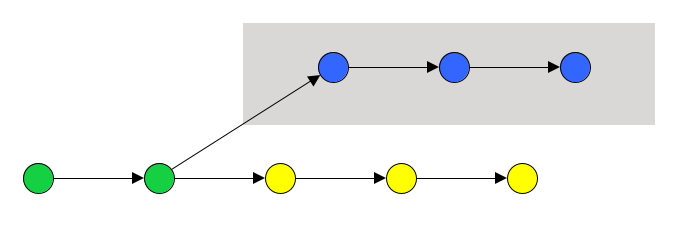
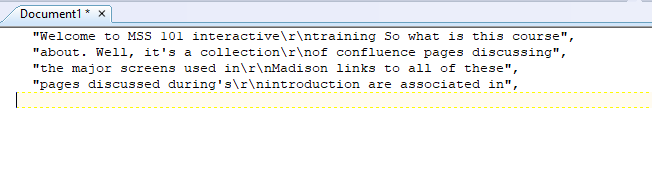
Each time-stamped bit of the transcript is in a separate set of quotes – I’ve got a quick replacement that takes
",\n "
And replaces it with a newline … so
Becomes
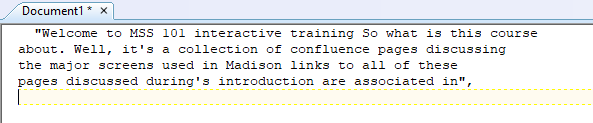
Depending on the target audience … for me, that’s where I stop. To send the transcript to someone else, I manually clean up the spaces and quote before the first line and the quote-comma on the last line.